See my previous blog post about flattr "How to help my projects?".

I added 20€ on my flattr account when I registered in 2010. At that time it was mandatory to add money on its flattr account.
Since that time I allocated a budget of 2€ per month, and I "reinvested" any received fund from flattr users in my flattr account. For the first time I do not have 2€ left on my account for the next month. I only have 0.87€.
Investments
In 4 years of using flattr I invested 2€ each month.That is 4 years x 2€ per month = 4 x 12 x 2€ = 96€ in total invested in flattr projects I support.
Results as of today (October 2014)
According to flattr:- You have done 406 flattrs in total
- You have given €98.79 in total to 45 creators
- You have received 195 flattrs in total
- Other users have 4 subscriptions active for your things
- You have received €80.36 in total from 53 supporters
The problem
According to flattr: "Creators receive 90% of the money you give."So 10% of the money you give do NOT got to creators and goes to flattr itself.
It could be fine but the system is closed and unless you are a very famous (and rich) creator you do not withdraw the money from flattr. So the money you receive is used to be given to other creators.
flattr gets 10% of the money you receive. And also 10% on the money you distribute, etc. After a few cycles in the system the money has all "evaporated" into the flattr account.
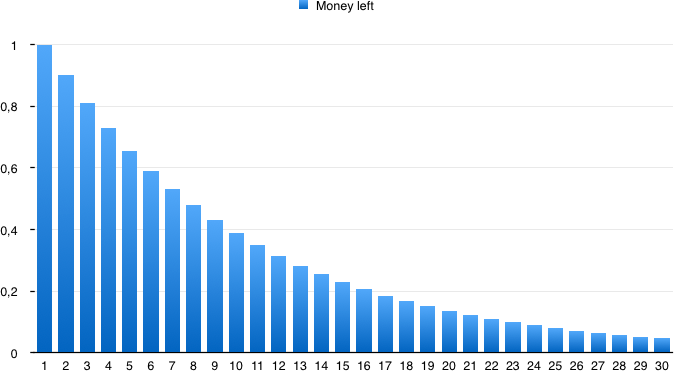
After 10 cycles, 61% of the money has "evaporated" as flattr taxes and only 39% is still available for creators.
After 24 cycles (2 years) only 9% of the initial money is still distributed to creators.
In that case only flattr is the winner in the story.
These numbers are only for the money your redistribute. If you have 10€ and only distribute 2€ each month then flattr will tax you 10% on the 2€, not on the 10€. But after 5 months at 2€ per month all your 10€ will be redistributed and then taxed.


